
Best MNO Core Network Solution: Revolutionizing Mobile Connectivity
2026-05-11
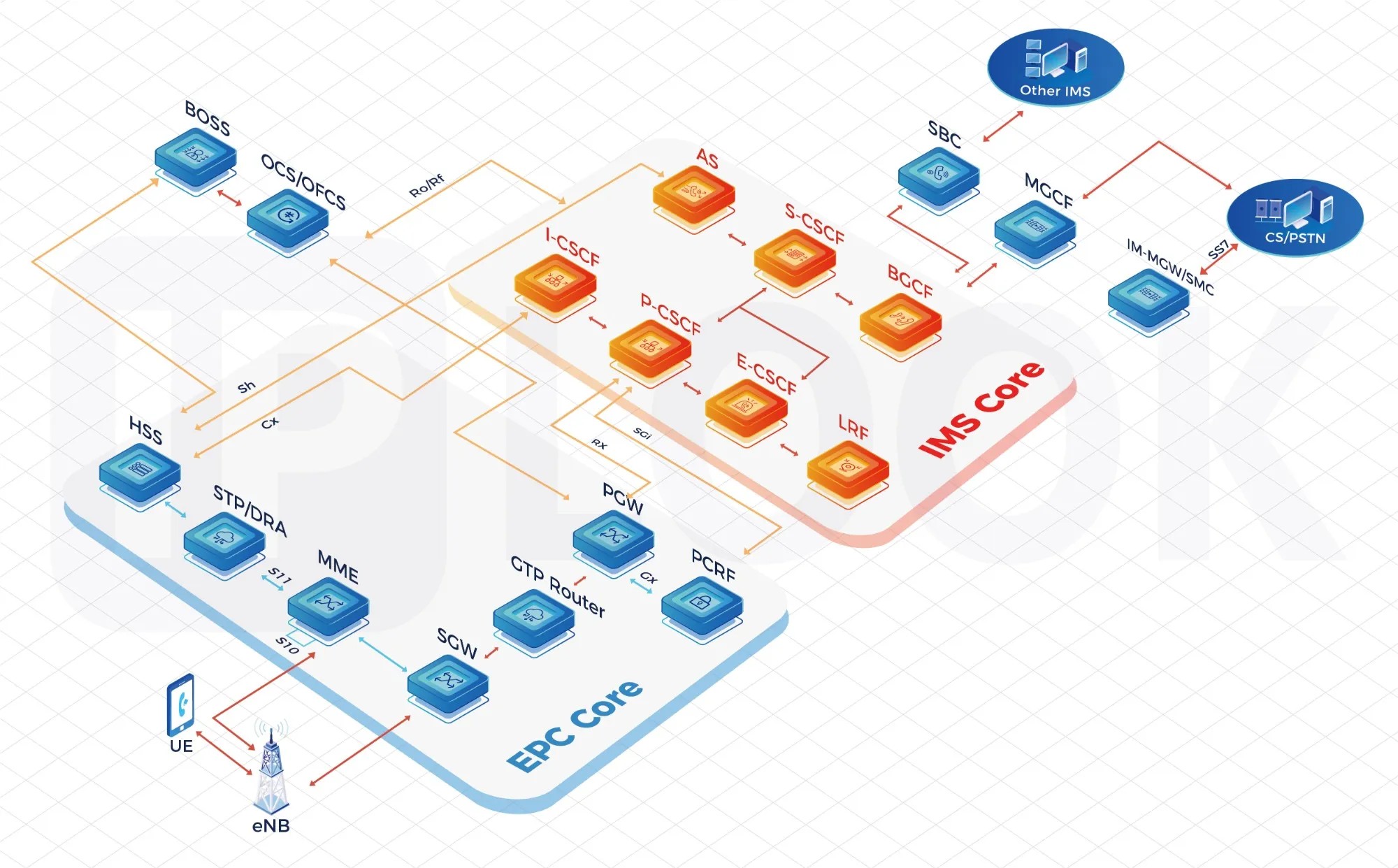
In an era where seamless connectivity defines everyday life, mobile network operators face mounting pressure to evolve. The core network stands as the backbone of every cellular service, yet many still rely on legacy systems that struggle to keep pace with soaring data demands and emerging 5G use cases. That's where IPLOOK steps in, reimagining what a core network can achieve. With a cloud-native, fully virtualized approach, IPLOOK's MNO core network solution doesn't just upgrade infrastructure—it revolutionizes how operators scale, monetize, and secure their networks for the future. But what truly sets it apart in a crowded market? Let's explore the technology that's rewriting the rules of mobile connectivity.
Unboxing the Invisible Network Backbone
We rarely stop to think about the colossal infrastructure that keeps our digital lives humming. Beneath every video call, every streamed movie, and every instant message lies a sprawling, mostly hidden mesh of fiber-optic cables, subsea routes, and anonymous switching centers. This is the network backbone—the unglamorous, yet indispensable, vascular system of the internet. Peeling back its layers reveals not just a marvel of engineering but a quietly negotiated patchwork of agreements and physical links that stitch the world together.
At the core are the invisible highways: hair-thin strands of glass pulsing with laser light across continents and under oceans. These are not the familiar server racks of a data center, but the buried, splashed, and sometimes shark-bitten cables that carry 99% of transoceanic traffic. Their paths are dictated by geography, politics, and cost—often shadowing old telegraph routes or railway lines. Unboxing this backbone means tracing the silent handshake between landing stations in quiet coastal towns and the bustling internet exchanges in major cities, where networks peer and barter for capacity.
What makes this skeleton so resilient yet so fragile? It’s a story of redundancy and single points of failure hidden in plain sight. While a construction crew might accidentally sever a cable and knock a region offline, the backbone’s self-healing protocols reroute traffic in milliseconds. From the physical layer upward, it’s a constant dance of trust and verification, where the invisible backbone not only carries our data but also defines the rhythm of modern connection—quietly, persistently, and almost magically out of view.
When Speed Meets Intelligence in the Core
In today's tech landscape, raw speed alone no longer defines excellence. When processing power is fused with adaptive intelligence within the core architecture, something remarkable happens. Tasks don't just complete faster—they complete smarter, anticipating needs and reallocating resources in real time. This synergy transforms a simple engine into a dynamic partner that learns and adjusts with every operation.
Consider a core that not only executes instructions but also understands context. As data flows in, intelligent algorithms within the core prioritize, cache, and predict, slashing latency without brute force. The result is a fluid experience where performance feels almost intuitive, cutting through complexity with grace rather than sheer horsepower. It's the difference between a tool that reacts and one that responds.
This marriage of speed and intelligence reshapes what's possible in everything from mobile devices to massive data centers. Instead of balancing trade-offs, we now get both immediacy and insight at the silicon level. The core becomes a hub of learning, where each cycle builds on the last, turning raw potential into tangible, context-aware performance that elevates the entire system.
Cloud-Native Agility: No More Hardware Headaches
Gone are the days of waiting weeks for server approvals, racking hardware, and wrestling with firmware updates. A cloud-native approach shifts the focus from maintaining physical infrastructure to building and iterating on applications. Instead of capacity planning spreadsheets and late-night alerts about failing drives, teams can provision environments on demand and scale them with a single command. This freedom transforms the pace of development, turning what used to be a multi-month hardware procurement cycle into a matter of minutes.
The real relief comes from offloading the undifferentiated heavy lifting—power, cooling, networking, and hardware lifecycle management—to the cloud provider. Engineers no longer need to interrupt feature work for bare-metal troubleshooting or patching hypervisors. Containers and serverless platforms abstract away the OS and runtime, letting teams ship code without worrying about the machine underneath. This not only reduces operational toil but also slashes the risk of human error that often creeps in during manual server configurations.
Perhaps the most underrated benefit is the mental shift. When hardware stops being a bottleneck, teams stop thinking in terms of fixed resources and start designing for resilience and elasticity. Deployments become routine, rollbacks painless, and experimentation cheaper. The result is a culture where trying new ideas doesn’t mean filling out a purchase order—it means spinning up a cluster, testing a hypothesis, and tearing it down just as easily.
Slicing Through the Noise: Custom Networks at Scale
Building custom networks capable of slicing through information overload requires more than just adding layers. At scale, the real challenge is maintaining signal fidelity while handling massive, noisy data streams. Our approach focuses on dynamic topology adaptation—networks that learn to prune irrelevant connections and amplify meaningful patterns without manual tuning. This isn't about one-size-fits-all architectures; it's about designing systems that evolve with the data they process, ensuring that scale doesn't come at the cost of clarity.
What sets this apart is the emphasis on operational efficiency. Instead of throwing more compute at the problem, we embed noise-suppression logic directly into the network's training cycle. The result is a streamlined model that outperforms generic alternatives, particularly in environments where precision matters most. By keeping the architecture lean and purpose-driven, these custom networks deliver consistent performance even as demand surges—quietly making sense of the chaos without exhausting resources.
Fort Knox for Mobile Data: Redesigning Trust
Mobile devices hold the keys to our digital lives, yet their security often feels like a bank vault with a screen door. We've wrapped sensitive data in layers of encryption and biometric locks, but the foundation of trust remains shaky because it's still built on blind acceptance of the operating system's integrity. True redesign isn't about adding more locks; it's about subverting the assumption that any single layer can be trusted completely. By decoupling data protection from the OS itself, we force even a compromised kernel to negotiate with a physically isolated secure element for every decryption request, rendering silent data exfiltration useless.
This shift flips the traditional permission model on its head. Instead of granting apps access to your files and hoping they behave, the data enforces its own rules at the silicon level. Photos, messages, and payment credentials become self-protecting artifacts that can't be unwrapped without a chain of cryptographic consent extending from the secure enclave to your explicit biometric confirmation. The mobile device stops being a passive storage locker and becomes an active defense grid where trust isn't assumed—it's continuously verified in real time.
What emerges is a blueprint for ambient security that follows the data, not the device. When even the service provider can't access your plaintext because the encryption keys are hardware-bound and never leave the device, the entire notion of a "data breach" requires redefinition. Redesigning trust for mobile data means we stop chasing enemies out of the fortress and instead make the treasure impossible to steal, no matter how deep an attacker tunnels.
From Operator to Experience Curator
The shift from running a service to designing moments is subtle but profound. It’s not about checking tasks off a list anymore—it’s about sensing the mood in the room, timing the small surprises, and letting curiosity lead the way. You stop managing logistics and start layering meaning into every interaction, turning the ordinary into something worth remembering.
This new role asks for a different kind of attention. Instead of optimizing for efficiency, you’re tuning into what feels right for the people in front of you. A carefully chosen detail—a handwritten note, an unexpected detour, a story shared at just the right moment—can transform a standard routine into a personal narrative. The curator doesn’t just deliver; they craft atmospheres and gently guide emotions.
The real magic happens when you embrace the unknown alongside your guests. You’re not performing a script but co-creating a journey, responding to the energy in real time. It’s about being present enough to spot opportunities for delight and brave enough to follow them, even if they break the plan. In the end, you’re remembered not for what you managed, but for how you made people feel.
FAQ
It provides a fully virtualized, cloud-native architecture that streamlines operations and slashes infrastructure costs. Operators can scale services on demand without hardware overhaul, while automated orchestration cuts down manual configuration time dramatically.
By pushing intelligence to the edge and optimizing data routing, latency drops significantly. The system dynamically adjusts to traffic patterns, so users experience fewer dropped connections and more consistent speeds even in crowded areas.
Absolutely. It integrates network slicing at a granular level, allowing dedicated virtual networks for different use cases on the same physical infrastructure. Built-in AI-driven analytics predict and resolve congestion before it impacts service.
Users notice faster app loading, smoother video streaming, and near-instant response in gaming. Beyond raw speed, the reliability means voice calls don't cut out and IoT devices maintain steady connections.
It's designed with modularity in mind, so smaller players can adopt exactly what they need without overspending. The pay-as-you-grow model makes enterprise-grade connectivity accessible to regional operators breaking into new markets.
It tackles vendor lock-in by embracing open standards, simplifies maintenance through centralized software control, and resolves the capacity crunch by efficiently using spectrum and backhaul resources.
The architecture inherently supports 5G standalone mode and seamless integration with existing 4G/LTE. It's built to evolve, accommodating future releases like 6G through software updates rather than forklift upgrades.
Conclusion
Modern mobile networks demand a core that does more than just connect calls—it must orchestrate a seamless, intelligent experience. At the heart of this revolution lies an invisible backbone that moves beyond legacy hardware, embracing a cloud-native architecture that turns rigid infrastructure into fluid, dynamic services. This shift eliminates hardware headaches, allowing operators to deploy updates in seconds rather than months, and unlocks a new realm where speed meets intelligence. The core becomes a living brain, analyzing traffic in real time, predicting congestion, and adapting on the fly to ensure every interaction feels instantaneous and effortless.
But true transformation comes when networks become deeply personal and inherently trustworthy. With advanced slicing, a single physical network can spawn countless virtual networks, each tailored to a specific need—whether it's ultra-reliable connections for autonomous vehicles or massive bandwidth for live streaming events. Meanwhile, trust is redesigned from the ground up, embedding security into every layer so that user data remains as impenetrable as a fortress. This fusion of flexibility, security, and insight redefines the operator’s role from a simple connectivity provider to an experience curator, shaping digital moments that feel bespoke, reliable, and revolutionary.
Contact Us
Contact Person: Shimmy
Email: [email protected]
Tel/WhatsApp: 85253392231
Website: https://www.iplook.com

